As companies and developers continue to build and proliferate fintech API dev docs, we will see continuous disintermediation of traditional financial institutions and part of their functionalities they provide to customers. Along with this comes an immediate need to better manage data privacy given the constant transmission of data and payment between different consumer/business finance data aggregator (i.e. Plaid), debit payment facilitator (i.e. Stripe, Modern Treasury, Treasury Prime) and credit payment facilitator (i.e. Method).
Skyflow is an industry-agnostic, data privacy API-first focused company (from healthcare data with HIPAA to fintech payment data to any industry that falls under US Dept of Commerce-NIST “Guide to Protecting the Confidentiality of Personally Identifiable Information (PII)).
Some takeaways from their data privacy API dev docs that any companies can use part or all of the essences here to their data privacy strategies:
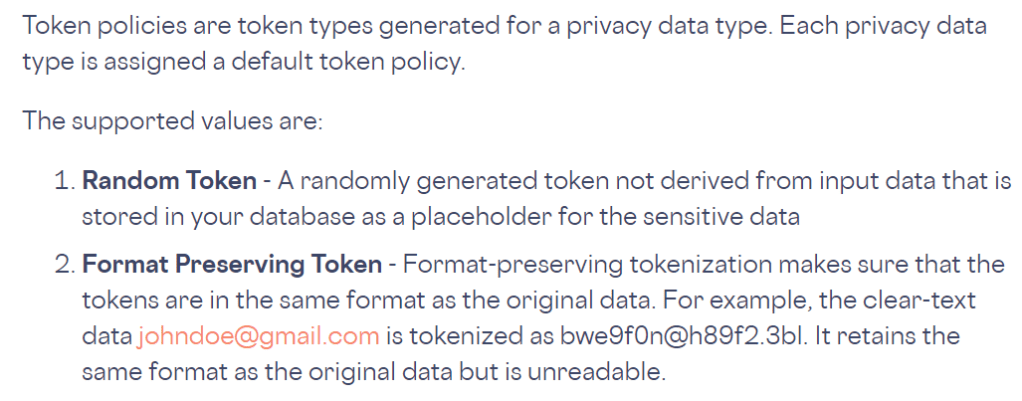
- Reduce PCI and other compliance scope by offloading sensitive data from your systems to Skyflow using tokenization or other common design patterns. Each data set or data type can be another layer of security with either and/or a random token (randomized series of token code) or format preserving token (maintain the same/similar data structure for future reference/readability)
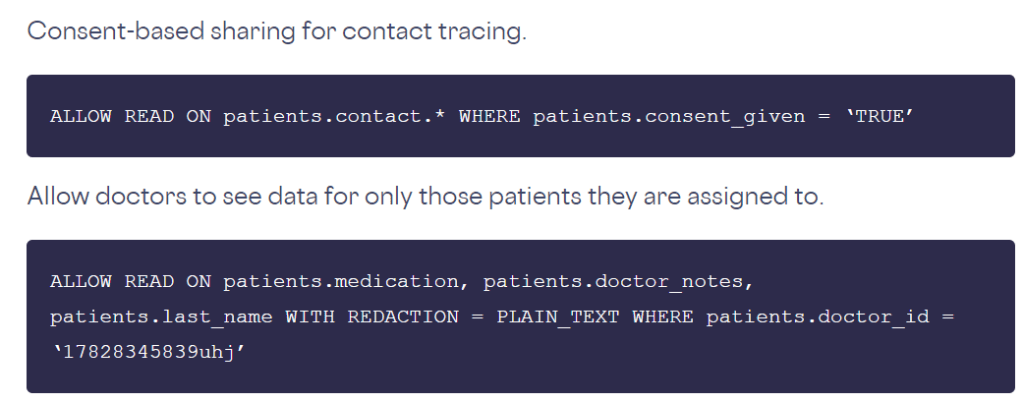
2. Internal and External Access Control layering by creating policy-based access control (PBAC), role-based access control (RBAC) and attribute-based access control (ABAC). These access control layers is determined by the operational and security compliance need of the business. For example, maybe the customer support staff will need policy-based access to have a CS-support team access with limited SSN # access in order to view last 4-digit of a customer SSN to do semi-manual compliance randomized secondary audit. Another example on external access control would be that patients would need to authorize and/or opted in to providing their personal healthcare data to another 3rd party (example of this below).
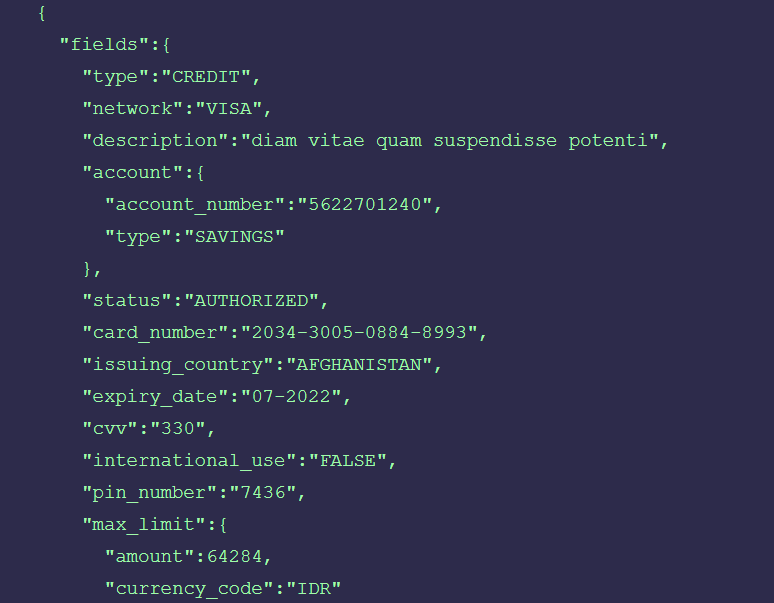
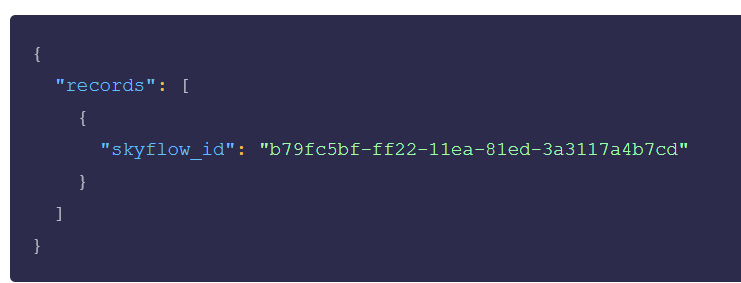
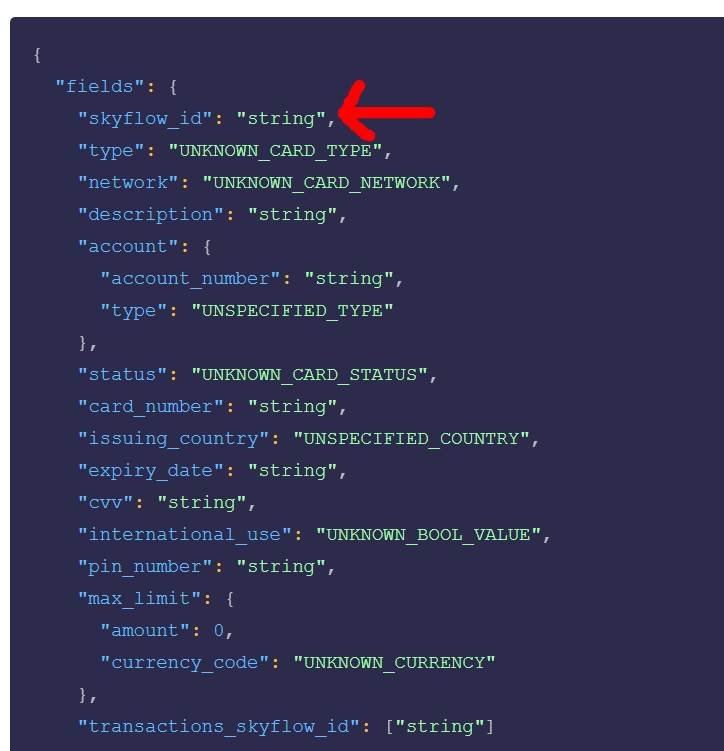
3. Payment Card Industry Data Security Standard (PCI) compliance need for businesses can be reduced substantially by storing sensitive customer and business financial data with 3rd parties such as Skyflow as they won’t be storing that data on their servers. Card information will be stored in Skyflow’s database like this (1st image below) and will be recorded in the system like this (2nd image below) which enables the data privacy protection to occur inside a relatively silo-ed environment and in order to retrieve the record in the future via API, the Skyflow ID will have to be provided (3rd image below).
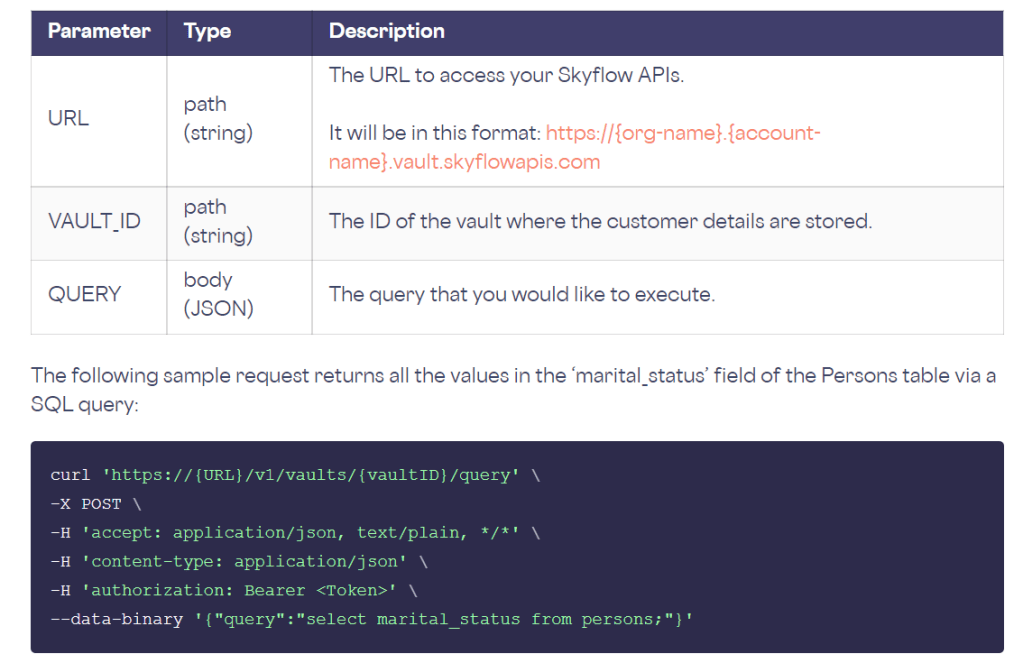
4. BI Tool and Dashboard with encrypted data could be a valuable tool for the mgmt team of the businesses that are building on top of Skyflow and the likes’ API to analyze and make strategic decisions of the business, operationally, financially and technically. In order to pull data from SF’s database, a VAULT_ID (in terms of logic tree, VAULT_ID is the top most layer, in essence these are Dropbox like storage for the business and subsequently, their customers’ data followed by SKYFLOW_ID, which are line items for each unique customer)
The query in the example below is to pull data from a specific VAULT_ID that contains the binary data ‘martial status’. It’s worth noting not all customer data can be pulled like this including customer credit card information, full SSN etc. The depth of these data pull is highly dependent on the sensitivity of these data based on the NIST(National Institute of Standards and Technology) guidelines.
Below is a macro overall of how SF manages their database infrastructure in terms data backup, incremental data backup, different time zone and fallback options for database in case of downtime, applying encryption on data backup, backup keys and access layer to these backup keys, and detailed observability and logging built-in for compliance and auditing purposes. Logs are retained in live storage for 30 days. After this retention period, logs are moved to archival storage are retained for up to seven years.
High-availability Infrastructure
I am definitely not a data privacy expert or API-oriented developer by trade but I enjoy reading and analyzing these API developer docs to help me and my team make a more informed decision on guiding the growth of the product from internal finance function-, product function- and overall company direction- perspective.